CodeCut
The intention of this project is to implement and analyze the CNM algorithm’s performance and the validity of its results compared to previous results obtained by other INSuRE teams. Provided time allows us to do so, we plan to implement the NCUT and DBScan algorithms and compare all three as a secondary objective.
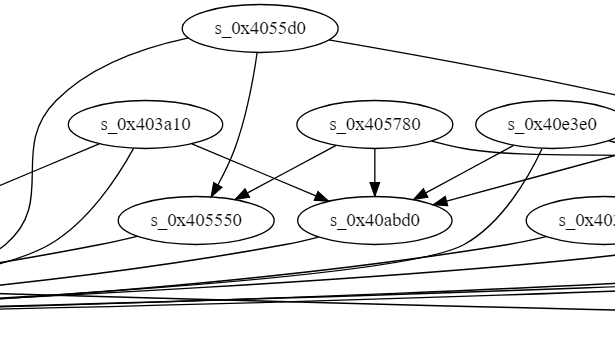
Since we started the project, we have been able to make tremendous progress. We first try to get an understanding of the problem and how to approach it. We then implemented the CNM algorithm with the snap library and run it through our dataset. While running the algorithm we were able to determine the graph structure which node and edges are link to each other. However, we can’t run the algorithm through large dataset.
Nowadays, cybersecurity is still a major concern in information technology field. It is related to every person’s daily life, every company’s business, and every country’s national security. Reverse engineering and binary analysis are widely used cybersecurity experts in analyzing malware and security vulnerabilities. Cybersecurity experts use many algorithms in binary analysis for analyzing function calls from machine code, such as CNM (Modularity) algorithm. In this project, we propose a way to analyze the accuracy of the CNM (Modularity) algorithm tested against the predetermined clusters of a programs call tree by testing new datasets and comparing our results with previous results.
Comments 0
No comments yet. Be the first to start the conversation!
Leave a Comment